ShmoopTube
Where Monty Python meets your 10th grade teacher.
Search Thousands of Shmoop Videos
Themes Videos
This video defines utopias and dystopias, and investigates how a utopia might become a dystopia. Can a seemingly perfect world actually be a dystopia in disguise?
Admiration Videos 9 videos
“Happy Hunger Games!” Or not. Katniss’s Hunger Games experiences left a not-so-happy effect on her. This video will prompt you to ponder if...
Why does Dr. Watson keep appearing in Sherlock Holmes's stories? Shmoop amongst yourselves.
Yes, there are kites. Yes, there are runners. No, despite how much we love running and flying kites, this isn't a happy story by any stretch of the...
Ambition Videos 5 videos
Appearances Videos 30 videos
Three scantily clad young girls enter a store. No, this isn’t your grandfather about to tell an inappropriate joke. And no, you’re not watching...
In Maya Angelou's poem "Africa," she compares Africa's pain and struggles to a woman being brutalized. Why does she do this? Is it to draw sympathy...
“Happy Hunger Games!” Or not. Katniss’s Hunger Games experiences left a not-so-happy effect on her. This video will prompt you to ponder if...
Art and Culture Videos 17 videos
Guy in a black leotard. In a cage. Not eating. Weird? Yes. Popular? Absolutely. Kafka's short story includes iconic artist-figures: a mouse singer...
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
We're not sure if good ol' Shakespeare would endorse The Bachelor and The Bachelorette, but that's not going to stop us from hosting themed viewing...
Betrayal Videos 10 videos
What is the American Dream? Is it popularity? Or is it being content with what you have? In Arthur Miller's play Death of a Salesman, the American...
The Grapes of Wrath is one of the longest—ahem, most important books in American literary history. But what's with the title?
Check out this video to find out why Wuthering Heights should never be considered #relationshipgoals.
Choices Videos 14 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
Ayn (rhymes with "mine," ironically enough) Rand penned this cult classic over 50 years ago, but it still resonates with today's audiences. Our que...
Imagine if dreams really could come true. This is the question that Langston Hughes ponders in his poem "Dream Deferred."
Civilization Videos 3 videos
Are humans civilized, or are we just savages waiting to come out? William Golding's novel Lord of the Flies tackles that question.
This video defines utopias and dystopias, and investigates how a utopia might become a dystopia. Can a seemingly perfect world actually be a dystop...
Having a fancy title has always been on our to-do list, but somehow being Lord of the Flies doesn't sound all that glamorous.
Coming of Age Videos 5 videos
Is Boo Radley the quintessential creep? Or, is he just isolated and misunderstood, hiding himself away to avoid people's judgment? You decide. He j...
Look, we get that you really like that one selfie with the makeup filter, but don't get this carried away about it, okay? Also, put your tongue bac...
What are the perks of being a wallflower? Shmoop amongst yourselves.
Compassion and Forgiveness Videos 26 videos
What? She gets a rose and we don’t? Who is this Emily person anyway? What’s she done to deserve such a delightful, aromatic gift?
No HBO? Well then, how does a horror short story writing contest sound? And the winner is...drum roll, please...Mary Shelley. You go, girl. And tha...
In To Kill a Mockingbird Scout is really, really not interested in learning about the so-called requirements of her gender. Even though she realize...
Contrasting Regions Videos 4 videos
We're not sure if good ol' Shakespeare would endorse The Bachelor and The Bachelorette, but that's not going to stop us from hosting themed viewing...
Could one of America’s most famous anti-slavery books be racist? Well, the book’s offensive caricatures combined with today’s perspective on...
The ultimate young-kid-lost-in-the-wilderness book. And yes, there are a lot of them.
Courage Videos 9 videos
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
In Markus Zusak's The Book Thief, Death narrates the story of one girl who lived during the Holocaust. Not surprisingly, it's kind of a downer—bu...
“Happy Hunger Games!” Or not. Katniss’s Hunger Games experiences left a not-so-happy effect on her. This video will prompt you to ponder if...
Criminality Videos 10 videos
In Markus Zusak's The Book Thief, Death narrates the story of one girl who lived during the Holocaust. Not surprisingly, it's kind of a downer—bu...
Crime and Punishment is all about a boy killing for money, literally, and then spending the rest of the book trying to hide it. Although the book c...
The Grapes of Wrath is one of the longest—ahem, most important books in American literary history. But what's with the title?
Death Videos 3 videos
Defeat Videos 2 videos
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
The Old Man and the Sea was actually Hemingway's second title. His editor wouldn't let him use The Middle Aged Man and the Stubborn Fish.
Determination Videos 2 videos
Whenever you start regretting the choices you've made in your life, just review Oedipus' story, and you'll start feeling a heck of a lot better.
Did you hear the one about the guy who killed his dad and married his mom? Yeah, that’s not a joke, it’s Oedipus’ life. This video summarizes...
Dissatisfaction Videos 10 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
Brave New World is supposed be an exciting book about a negative utopia and the corrupt powers of authority. So where’s the big car chase? What's...
Would would the world be like without books? Ray Bradbury tackles that question—and many more— in Fahrenheit 451. Go ahead; read it on your Kin...
Dreams, Hopes, and Plans Videos 18 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
What is the American Dream? Is it popularity? Or is it being content with what you have? In Arthur Miller's play Death of a Salesman, the American...
Drugs and Alcohol Videos 24 videos
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
Brave New World is supposed be an exciting book about a negative utopia and the corrupt powers of authority. So where’s the big car chase? What's...
Crime and Punishment is all about a boy killing for money, literally, and then spending the rest of the book trying to hide it. Although the book c...
Duty Videos 3 videos
Stephen Crane wrote The Red Badge of Courage about the Civil War not long after the war had ended. And get this: he didn't even fight in the war. W...
Pious Aeneas goes from minor character in the Trojan War to founder of Rome, the city that conquered the world, meetin' ladies and experiencing maj...
Pious Aeneas strikes again. This time, with more destiny and hand-to-hand combat! (Of course, since we're talking about Aeneas, he's still harping...
Education Videos 11 videos
This video covers the plot of Jane Eyre, a novel by Charlotte Brontë. In it, Jane Eyre, an orphan-turned-governess with a miserable childhood fall...
The Great Gatsby is set in and around New York City and Long Island. On the big L.I., there are two areas known as "West Egg" and "East Egg." East...
This video summarizes F. Scott Fitzgerald’s novel The Great Gatsby. Jay Gatsby goes from a rich party guy in love with a married woman to dead. W...
Exile Videos 4 videos
This video discusses the important ladies of The Sun Also Rises…make that the one important lady. Brett is the only major female character in the...
Boy and girl meet, fall in love, and commit suicide in a tomb. You know, your average love story.
Exploration Videos 10 videos
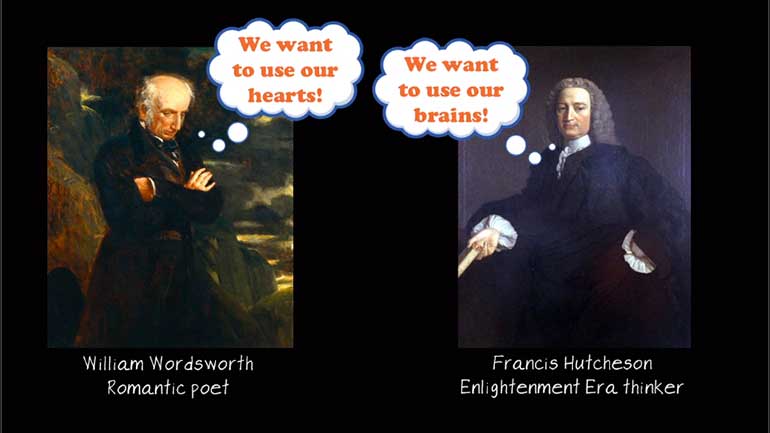
Imagine Frankenstein characters as zombie/werewolf hybrids: one side wants brains, the other hearts. How to choose? Also, what to name them? Zomwol...
We’ll preface this video about Frankenstein’s preface by saying that Mary Shelley is an awesome woman, and she wants everybody to be aware. Che...
Is Victor Frankenstein a: Romantic Hero? b: Byronic Hero? c: Satanic Hero? d: Guitar Hero? All of the above (but maybe not D…) We don�...
Family Videos 62 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
A family goes on a quest to bury their family member. Yeah, sounds simple...except it never is. ‘Cause mom’s dead, and people have issues which...
Fate and Free Will Videos 42 videos
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Why did the editor give Chapter 21 of A Clockwork Orange the axe? Was it because he wanted to leave the reader hanging? Or did he realize Americans...
No HBO? Well then, how does a horror short story writing contest sound? And the winner is...drum roll, please...Mary Shelley. You go, girl. And tha...
Fear Videos 20 videos
Have you ever pretended to be super happy for your BFF when they win an award when, really, you just wanted to rip it out of their undeserving, ung...
Ayn (rhymes with "mine," ironically enough) Rand penned this cult classic over 50 years ago, but it still resonates with today's audiences. Our que...
This video discusses the major ideas of the satirical American war novel Catch-22 by Joseph Heller. The horror of war meets…absurdity and humor?...
Foolishness and Folly Videos 17 videos
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
We're not sure if good ol' Shakespeare would endorse The Bachelor and The Bachelorette, but that's not going to stop us from hosting themed viewing...
Foreignness and 'The Other' Videos 20 videos
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
What is Dracula really about? Just Count Dracula? Or is there more to it than vampires? This video addresses some major ideas in Bram Stoker’s cl...
Freedom and Confinement Videos 14 videos
Brave New World is supposed be an exciting book about a negative utopia and the corrupt powers of authority. So where’s the big car chase? What's...
What is the American Dream? Is it popularity? Or is it being content with what you have? In Arthur Miller's play Death of a Salesman, the American...
Their eyes may have been watching God, but we think we know who won that staring contest.
Friendship Videos 27 videos
Have you ever pretended to be super happy for your BFF when they win an award when, really, you just wanted to rip it out of their undeserving, ung...
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Great Expectations by Charles Dickens is about a young blacksmith boy (Pip) and his two dreams: becoming a gentleman and marrying the beautiful Est...
Gender Videos 50 videos
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
Three scantily clad young girls enter a store. No, this isn’t your grandfather about to tell an inappropriate joke. And no, you’re not watching...
Good vs. Evil Videos 12 videos
The Salem Witch Trials in the 17th century. The Red Scare in the 1950s. Little to no evidence that witches/communists were anywhere close to taking...
The broken-hearted Abigail takes her revenge. You might never want to break-up with someone again after this video, so make sure the next person is...
One video to rule them all. One video to find them. One video to bring them all and in the darkness bind them. Or something like that. The Lord of...
Greed and Gluttony Videos 2 videos
The title is pretty ironic when you consider how little sleep you'd be getting if you had a headless horseman chasing you.
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
Guilt and Blame Videos 3 videos
How did Scrooge go from being naughty to nice so quickly, and why? (Hint: contrary to popular belief, it has nothing to do with the ghost of Santa...
Puritan adultery=big scarlet “A.” Puritan's know how to keep it simple. What’s not so simple? Hester Prynne’s adamant refusal to reveal who...
This video provides a summary of the dystopian novel Divergent. It covers Beatrice Prior’s path from discovering she is Divergent (doesn’t fit...
Happiness Videos 3 videos
Ayn (rhymes with "mine," ironically enough) Rand penned this cult classic over 50 years ago, but it still resonates with today's audiences. Our que...
"Nothing cared I that time would take me": the famous words of Dylan Thomas in his poem "Fern Hill." In this poem, the speaker fights age and aims...
Can you really learn about human nature by removing yourself from the company of other humans? Henry David Thoreau thought it was a possibility and...
Hate Videos 7 videos
Kaffir Boy is the story of a young South African tennis player living under the restrictions of apartheid. He ends up going the self-preservation r...
A word to the wise: secret marriages don't work out well in Shakespeare plays. Just ask Othello and Desdemona.
Hunger Videos 1 videos
The Old Man and the Sea was actually Hemingway's second title. His editor wouldn't let him use The Middle Aged Man and the Stubborn Fish.
Identity Videos 37 videos
Have you ever pretended to be super happy for your BFF when they win an award when, really, you just wanted to rip it out of their undeserving, ung...
Written in Anglo-Saxon, or Old English, sometime between the 8th and 11th centuries, Beowulf is an epic poem that reflects the early medieval warri...
In Markus Zusak's The Book Thief, Death narrates the story of one girl who lived during the Holocaust. Not surprisingly, it's kind of a downer—bu...
Innocence Videos 14 videos
Are humans civilized, or are we just savages waiting to come out? William Golding's novel Lord of the Flies tackles that question.
Having a fancy title has always been on our to-do list, but somehow being Lord of the Flies doesn't sound all that glamorous.
Isolation Videos 32 videos
Guy in a black leotard. In a cage. Not eating. Weird? Yes. Popular? Absolutely. Kafka's short story includes iconic artist-figures: a mouse singer...
What? She gets a rose and we don’t? Who is this Emily person anyway? What’s she done to deserve such a delightful, aromatic gift?
Brave New World is supposed be an exciting book about a negative utopia and the corrupt powers of authority. So where’s the big car chase? What's...
Jealousy Videos 8 videos
Have you ever pretended to be super happy for your BFF when they win an award when, really, you just wanted to rip it out of their undeserving, ung...
Their eyes may have been watching God, but we think we know who won that staring contest.
Justice and Judgement Videos 20 videos
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
Historical fiction novels like The Help can whisk you back to a place and time that you may have only read about in history books. Or... a place an...
Crime and Punishment is all about a boy killing for money, literally, and then spending the rest of the book trying to hide it. Although the book c...
Language and Communication Videos 38 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
Lies and Deceit Videos 48 videos
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
What is the American Dream? Is it popularity? Or is it being content with what you have? In Arthur Miller's play Death of a Salesman, the American...
Life, Consciousness, and Existence Videos 22 videos
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
No HBO? Well then, how does a horror short story writing contest sound? And the winner is...drum roll, please...Mary Shelley. You go, girl. And tha...
Can you really learn about human nature by removing yourself from the company of other humans? Henry David Thoreau thought it was a possibility and...
Literature and Writing Videos 23 videos
Historical fiction novels like The Help can whisk you back to a place and time that you may have only read about in history books. Or... a place an...
In Markus Zusak's The Book Thief, Death narrates the story of one girl who lived during the Holocaust. Not surprisingly, it's kind of a downer—bu...
Brave New World is supposed be an exciting book about a negative utopia and the corrupt powers of authority. So where’s the big car chase? What's...
Love Videos 61 videos
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
We're not sure if good ol' Shakespeare would endorse The Bachelor and The Bachelorette, but that's not going to stop us from hosting themed viewing...
Loyalty Videos 13 videos
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
Luck Videos 1 videos
The Old Man and the Sea was actually Hemingway's second title. His editor wouldn't let him use The Middle Aged Man and the Stubborn Fish.
Madness Videos 16 videos
Man and the Natural World Videos 35 videos
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Would would the world be like without books? Ray Bradbury tackles that question—and many more— in Fahrenheit 451. Go ahead; read it on your Kin...
Manipulation Videos 15 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
“Happy Hunger Games!” Or not. Katniss’s Hunger Games experiences left a not-so-happy effect on her. This video will prompt you to ponder if...
Marriage Videos 32 videos
In The Color Purple, Celie is abused by her father and husband. She leaves her father by marrying Mr. ________, and then leaves Mr. ______, too. Bu...
What is Dracula really about? Just Count Dracula? Or is there more to it than vampires? This video addresses some major ideas in Bram Stoker’s cl...
Meet Emma Woodhouse of Jane Austen's Emma. She’s a rich young woman with a good social life living in 18th-century England. We bet she has an aw...
Memory and the Past Videos 26 videos
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
What? She gets a rose and we don’t? Who is this Emily person anyway? What’s she done to deserve such a delightful, aromatic gift?
Men and Masculinity Videos 7 videos
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
This video discusses the important ladies of The Sun Also Rises…make that the one important lady. Brett is the only major female character in the...
Stephen Crane wrote The Red Badge of Courage about the Civil War not long after the war had ended. And get this: he didn't even fight in the war. W...
Morality and Ethics Videos 26 videos
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
Written in Anglo-Saxon, or Old English, sometime between the 8th and 11th centuries, Beowulf is an epic poem that reflects the early medieval warri...
Mortality Videos 20 videos
Life of Pi tells the story of a boy and a tiger trapped on a lifeboat for 227 days... or does it?
Their eyes may have been watching God, but we think we know who won that staring contest.
The Great Gatsby is set in and around New York City and Long Island. On the big L.I., there are two areas known as "West Egg" and "East Egg." East...
Passivity Videos 9 videos
Readers may be already be familiar with Dracula, but what about the mathematician and author, Bram Stoker? And yes, he graduated with a degree in m...
Vlad the Impaler was an appropriately named guy, until he went on tropical vacations. Then, he went by Vlad the Imtanner. For some facts that are a...
Looks, wealth, and a super cool castle to live in… Well...maybe not live in, if you happened to be Dracula. But for the most part, this guy had...
Perseverance Videos 7 videos
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
The ultimate young-kid-lost-in-the-wilderness book. And yes, there are a lot of them.
On his ten-year journey home from the Trojan War, Odysseus runs into everything from sirens to sea monsters to seductresses. Such is life when you...
Philosophical Viewpoints Videos 7 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
We're not sure if good ol' Shakespeare would endorse The Bachelor and The Bachelorette, but that's not going to stop us from hosting themed viewing...
Philosophy Videos 5 videos
This video discusses the major ideas of the satirical American war novel Catch-22 by Joseph Heller. The horror of war meets…absurdity and humor?...
The Modernists thought the world had a lot of problems, and they were intent on fixing them—or at least talking about fixing them. Unfortunately,...
Politics Videos 16 videos
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
Gulliver's Travels is a classic tale of adventure with a dash of what-the-heck-is-happening thrown in for good measure.
Meet Charles Darnay, the nobleman who spends more time on trial and in prison than attending balls and drinking expensive wine. Don't feel too bad...
Poverty Videos 8 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
A family goes on a quest to bury their family member. Yeah, sounds simple...except it never is. ‘Cause mom’s dead, and people have issues which...
Power Videos 32 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
Prejudice Videos 7 videos
Is Boo Radley the quintessential creep? Or, is he just isolated and misunderstood, hiding himself away to avoid people's judgment? You decide. He j...
Under what circumstances should people be allowed to lie? Is Annemarie's situation dire enough? Shmoop amongst yourselves.
Pride Videos 20 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Primitivity Videos 5 videos
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Are humans civilized, or are we just savages waiting to come out? William Golding's novel Lord of the Flies tackles that question.
Having a fancy title has always been on our to-do list, but somehow being Lord of the Flies doesn't sound all that glamorous.
Principles Videos 11 videos
Three scantily clad young girls enter a store. No, this isn’t your grandfather about to tell an inappropriate joke. And no, you’re not watching...
How's Julius Caesar doing after that whole "assassination" thing? Well, he's taking it one day at a time.
On his ten-year journey home from the Trojan War, Odysseus runs into everything from sirens to sea monsters to seductresses. Such is life when you...
Race Videos 30 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
Historical fiction novels like The Help can whisk you back to a place and time that you may have only read about in history books. Or... a place an...
In The Color Purple, Celie is abused by her father and husband. She leaves her father by marrying Mr. ________, and then leaves Mr. ______, too. Bu...
Rebellion Videos 5 videos
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
Imagine a world in which all literature was dystopian. Okay, so we may be getting to that point, 1984 and V for Vendetta helped start it all.
Religion Videos 47 videos
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
A family goes on a quest to bury their family member. Yeah, sounds simple...except it never is. ‘Cause mom’s dead, and people have issues which...
Repression Videos 5 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
Dig up your trench coat, grab your magnifying glass, and stick on that fake mustache (we know you have one): it's time to unleash your inner Sherlo...
Respect and Reputation Videos 16 videos
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Meet Emma Woodhouse of Jane Austen's Emma. She’s a rich young woman with a good social life living in 18th-century England. We bet she has an aw...
Stephen Crane wrote The Red Badge of Courage about the Civil War not long after the war had ended. And get this: he didn't even fight in the war. W...
Revenge Videos 24 videos
No HBO? Well then, how does a horror short story writing contest sound? And the winner is...drum roll, please...Mary Shelley. You go, girl. And tha...
In the world of Shakespeare, pretty much everyone either dies or gets married. Hamlet and co. got the short end of that stick.
Rules and Order Videos 12 videos
Have you ever pretended to be super happy for your BFF when they win an award when, really, you just wanted to rip it out of their undeserving, ung...
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
Would would the world be like without books? Ray Bradbury tackles that question—and many more— in Fahrenheit 451. Go ahead; read it on your Kin...
Sacrifice Videos 18 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
No HBO? Well then, how does a horror short story writing contest sound? And the winner is...drum roll, please...Mary Shelley. You go, girl. And tha...
Science Videos 12 videos
This video summarizes the plot of Brave New World from the point of view of John (you know, the “savage”). It covers the escapism, social casts...
Wait. The monster’s name isn’t Frankenstein? Mind. Blown. Watch the video to find out more about Dr. Frankenstein’s nameless monster.
Imagine Frankenstein characters as zombie/werewolf hybrids: one side wants brains, the other hearts. How to choose? Also, what to name them? Zomwol...
Secrecy Videos 11 videos
Wait. The monster’s name isn’t Frankenstein? Mind. Blown. Watch the video to find out more about Dr. Frankenstein’s nameless monster.
Imagine Frankenstein characters as zombie/werewolf hybrids: one side wants brains, the other hearts. How to choose? Also, what to name them? Zomwol...
We’ll preface this video about Frankenstein’s preface by saying that Mary Shelley is an awesome woman, and she wants everybody to be aware. Che...
Sex Videos 32 videos
Ayn (rhymes with "mine," ironically enough) Rand penned this cult classic over 50 years ago, but it still resonates with today's audiences. Our que...
Brave New World is supposed be an exciting book about a negative utopia and the corrupt powers of authority. So where’s the big car chase? What's...
This video discusses the major ideas of the satirical American war novel Catch-22 by Joseph Heller. The horror of war meets…absurdity and humor?...
Sexuality and Sexual Identity Videos 7 videos
In The Color Purple, Celie is abused by her father and husband. She leaves her father by marrying Mr. ________, and then leaves Mr. ______, too. Bu...
The Catcher in the Rye tells the story of Holden Caulfield’s Worst Weekend Ever, and this video tells the story of that story. From losing the fe...
Sin Videos 2 videos
All Okonkwo was asking for was a little R-E-S-P-E-C-T. Granted, swinging your machete around may not be the nicest way to ask, but still. The guy d...
Slavery Videos 1 videos
Could one of America’s most famous anti-slavery books be racist? Well, the book’s offensive caricatures combined with today’s perspective on...
Society and Class Videos 40 videos
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
It may be the best of times for Chuck Darnay, but it's pretty much constantly the worst of times for Sydney. Poor guy.
Three scantily clad young girls enter a store. No, this isn’t your grandfather about to tell an inappropriate joke. And no, you’re not watching...
Suffering Videos 29 videos
Guy in a black leotard. In a cage. Not eating. Weird? Yes. Popular? Absolutely. Kafka's short story includes iconic artist-figures: a mouse singer...
We were so moved by Angelina Jolie's overseas adoptions that we created a proposal to bring foreign-born children over by the thousands! Think abou...
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
Technology and Modernization Videos 22 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
What is Dracula really about? Just Count Dracula? Or is there more to it than vampires? This video addresses some major ideas in Bram Stoker’s cl...
The Home Videos 18 videos
This video summarizes the play A Raisin in the Sun. It discusses the Youngers, members of an African-American family trying to better themselves wh...
Historical fiction novels like The Help can whisk you back to a place and time that you may have only read about in history books. Or... a place an...
Crime and Punishment is all about a boy killing for money, literally, and then spending the rest of the book trying to hide it. Although the book c...
The Supernatural Videos 22 videos
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
Written in Anglo-Saxon, or Old English, sometime between the 8th and 11th centuries, Beowulf is an epic poem that reflects the early medieval warri...
If you suddenly came into a bunch of money, you'd give it all away, right? Yeah, we figured.
Time Videos 10 videos
Great Expectations by Charles Dickens is about a young blacksmith boy (Pip) and his two dreams: becoming a gentleman and marrying the beautiful Est...
Samuel Taylor Coleridge's "Kubla Khan" is like one long drug trip. Don't try this at home.
This video summarizes the Shakespearean play Macbeth. Two major forces are at play in the story: witches’ prophecies and Macbeth’s demanding wi...
Tradition and Customs Videos 19 videos
Written in Anglo-Saxon, or Old English, sometime between the 8th and 11th centuries, Beowulf is an epic poem that reflects the early medieval warri...
"Girl," by Jamaica Kincaid, is a poem—er, a story... er... what is this thing? Either way, it's about a mother's advice to her daughter. And noth...
In Julie of the Wolves, a girl is thrown into the wild, far away from civilization. Find out how she fares by watching this video.
Transformation Videos 16 videos
In Maya Angelou's poem "Africa," she compares Africa's pain and struggles to a woman being brutalized. Why does she do this? Is it to draw sympathy...
We're not sure if good ol' Shakespeare would endorse The Bachelor and The Bachelorette, but that's not going to stop us from hosting themed viewing...
Why did the editor give Chapter 21 of A Clockwork Orange the axe? Was it because he wanted to leave the reader hanging? Or did he realize Americans...
Transience Videos 4 videos
Boy and girl meet, fall in love, and commit suicide in a tomb. You know, your average love story.
Truth Videos 1 videos
The title is pretty ironic when you consider how little sleep you'd be getting if you had a headless horseman chasing you.
Versions of Reality Videos 19 videos
Aren't midsummer night dreams the worst? You wake up all sweaty and gross, and for a minute there, you can't even remember where you are. And also,...
What? She gets a rose and we don’t? Who is this Emily person anyway? What’s she done to deserve such a delightful, aromatic gift?
A family goes on a quest to bury their family member. Yeah, sounds simple...except it never is. ‘Cause mom’s dead, and people have issues which...
Violence Videos 31 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
How do you insult the Soviet Union and get away with it? Make them animals. (No one will ever know.) That was George Orwell's plan, and it worked....
Visions of America Videos 13 videos
What? She gets a rose and we don’t? Who is this Emily person anyway? What’s she done to deserve such a delightful, aromatic gift?
Ayn (rhymes with "mine," ironically enough) Rand penned this cult classic over 50 years ago, but it still resonates with today's audiences. Our que...
What is the American Dream? Is it popularity? Or is it being content with what you have? In Arthur Miller's play Death of a Salesman, the American...
War and Warfare Videos 27 videos
Well, if this book doesn't make you want to tape over your laptop camera, we don't know what will.
By the end of this video, you will be brainwashed. There's nothing you can do about it; we just wanted to let you know. We like to think we're bigg...
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
Weakness Videos 3 videos
This video provides a summary of John Steinbeck’s Of Mice and Men. When George and Lennie find new work during the Great Depression, fights, frie...
Why does Dr. Watson keep appearing in Sherlock Holmes's stories? Shmoop amongst yourselves.
Wealth Videos 21 videos
Written in Anglo-Saxon, or Old English, sometime between the 8th and 11th centuries, Beowulf is an epic poem that reflects the early medieval warri...
Meet Emma Woodhouse of Jane Austen's Emma. She’s a rich young woman with a good social life living in 18th-century England. We bet she has an aw...
The Grapes of Wrath is one of the longest—ahem, most important books in American literary history. But what's with the title?
Wisdom and Knowledge Videos 12 videos
A cheap shot at a bestseller or a deeper book with connections relevant to the human race? In The Call of the Wild, the protagonist is a dog named...
Would would the world be like without books? Ray Bradbury tackles that question—and many more— in Fahrenheit 451. Go ahead; read it on your Kin...
Women and Femininity Videos 24 videos
You might be hearing a chorus of farewells if you recommend A Farewell to Arms as the next read for your Fabulously Feisty Feminist Book Club.
A family goes on a quest to bury their family member. Yeah, sounds simple...except it never is. ‘Cause mom’s dead, and people have issues which...
In The Color Purple, Celie is abused by her father and husband. She leaves her father by marrying Mr. ________, and then leaves Mr. ______, too. Bu...
Youth Videos 14 videos
Have you ever pretended to be super happy for your BFF when they win an award when, really, you just wanted to rip it out of their undeserving, ung...
She was just a girl who found herself in some unimaginably awful circumstances. If you feel like gaining some valuable perspective on the drama in...